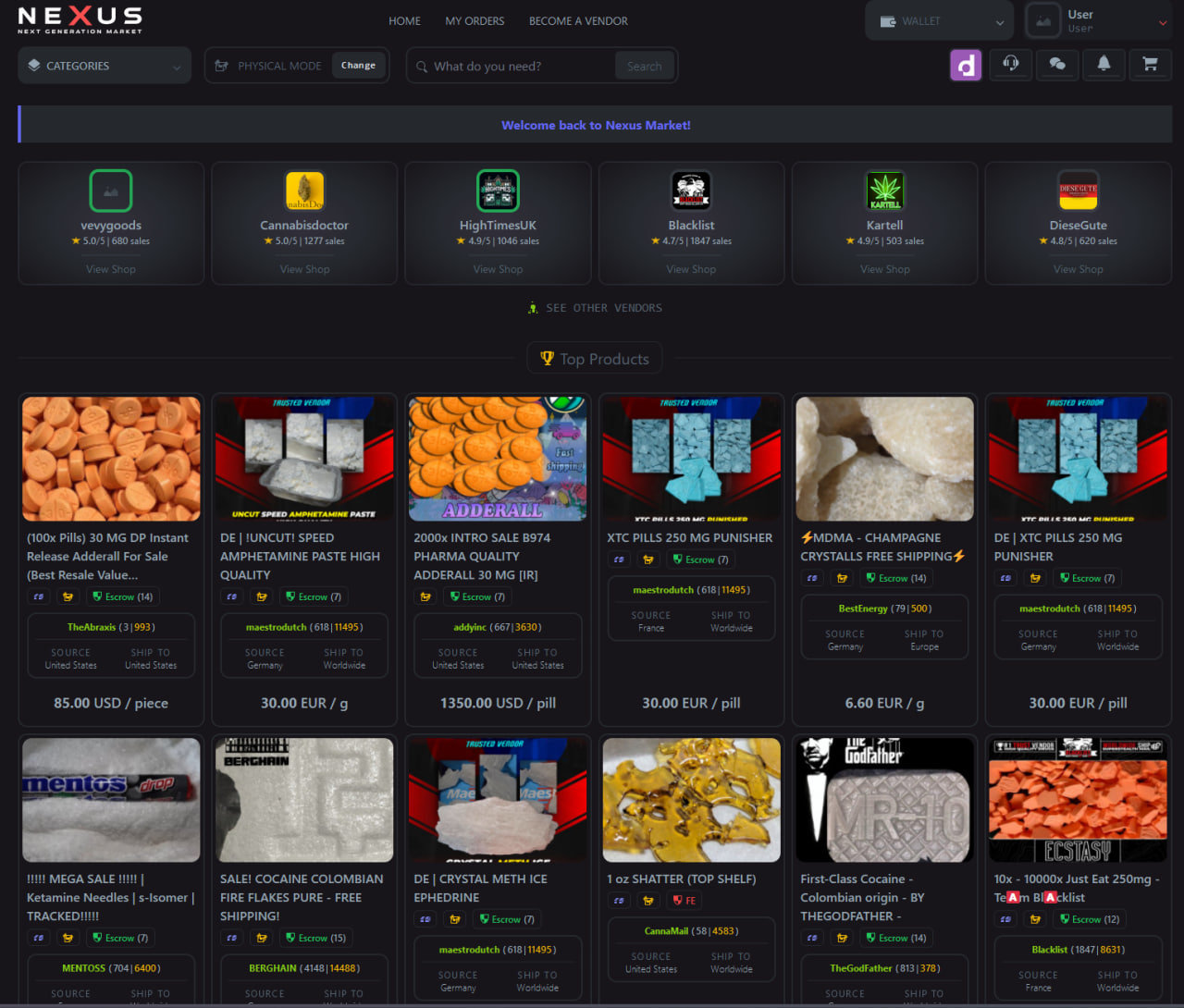
WHAT IS NEXUS MARKET AND HOW DOES IT OPERATE?
Nexus Market is a well-documented anonymous trading platform operating exclusively on the Tor network. According to cybersecurity research firms and academic studies, it follows the standard darknet marketplace structure: a web-based interface accessible only through Tor Browser, a vendor registration system, and an escrow-based transaction layer.
The platform enforces PGP encryption for all private communications between buyers and vendors, consistent with privacy-first marketplace architecture documented in peer-reviewed information-security literature. Vendor accounts require a deposit and identity verification through the platform's badge system, which assigns trust tiers based on transaction history and community feedback.
Research into darknet marketplace ecosystems consistently places the anonymous marketplace category as a persistent feature of the Tor landscape. The Nexus Darknet platform has been cited in multiple threat intelligence briefings as a significant node in this ecosystem, with operational continuity maintained through redundant onion relay architecture.
Key Platform Characteristics
- Accessible exclusively via Tor Browser (.onion domain)
- No clearnet mirror — Tor-only access enforced at network level
- PGP-2048 minimum encryption for all vendor communications
- Multi-signature escrow transactions (standard and FE options)
- Three accepted cryptocurrencies: XMR, BTC, LTC
- Vendor bond deposit with tiered verification levels
- Dispute resolution arbitration by platform moderators
- No-JavaScript interface option for maximum anonymity
- CAPTCHA on all login forms to prevent automated access
For a complete breakdown of Nexus Market features and platform architecture, see the dedicated information page.

Anonymous Access
Operates exclusively over Tor with no clearnet exposure. IP addresses are never logged. JavaScript-free browsing mode available for maximum anonymity.

Escrow Protection
Multi-signature escrow holds funds until delivery is confirmed. Disputes trigger third-party arbitration. Finalize-Early option available for trusted vendors.

Vendor Verification
Tiered badge system assigns trust scores based on transaction volume, reviews, and bond deposits. Level 1 through Level 5 vendor tiers documented publicly.

PGP Encryption
All communications between platform users require PGP key exchange. 2048-bit minimum key length enforced. Automated encryption built into the messaging interface.

Multi-Currency
Accepts Monero (XMR), Bitcoin (BTC), and Litecoin (LTC). Monero is the recommended option for maximum transaction privacy due to its ring-signature protocol.

Dispute Resolution
Structured arbitration process allows buyers and vendors to submit evidence. Moderators review cases within documented SLA timeframes based on transaction value.
CRYPTOCURRENCY & ANONYMOUS TRANSACTIONS
Cryptocurrency became the default transaction medium for privacy-focused online markets following Bitcoin's emergence in 2009. Early markets relied on Bitcoin's pseudonymous properties, but blockchain analysis tools gradually eroded its practical anonymity. This gap prompted the development of privacy-specific currencies designed to resist chain analysis by default.
Privacy coins introduce cryptographic techniques — ring signatures, stealth addresses, and zero-knowledge proofs — that obscure transaction participants and amounts at the protocol level. The detailed cryptocurrency guide on this site covers the technical foundations of each accepted coin and the privacy trade-offs involved.
Ring signatures, RingCT, and stealth addresses make Monero transactions untraceable by design. Recommended for maximum privacy. Full XMR guide →
The original pseudonymous currency. Requires additional privacy layers (CoinJoin, Lightning Network) for darknet research use. Full BTC guide →
Faster confirmation times than BTC. Lower fees make it suitable for smaller transactions. Still requires privacy practices for anonymous use. Full LTC guide →
LATEST MARKET NEWS & UPDATES

April 04, 2026
Nexus Market Q1 2026: Platform Statistics Released
Q1 2026 data shows continued growth across all platform metrics, with Monero transactions reaching a new quarterly record.
READ MORE →
March 21, 2026
OPSEC Update: New Threat Vectors Identified in 2026
Security researchers have documented emerging deanonymization vectors. Updated countermeasures and best practices analyzed.
READ MORE →
March 07, 2026
Enhanced 2FA on Nexus Market: Security Upgrade Analysis
The platform rolled out upgraded two-factor authentication protocols. Technical analysis of the implementation and security implications.
READ MORE →
February 21, 2026
XMR Adoption Metrics: Darknet Transaction Privacy in 2026
Monero's share of anonymous marketplace transactions reached new highs in early 2026. On-chain data and analysis reviewed.
READ MORE →
February 07, 2026
Nexus Market PGP Infrastructure Update: February 2026
Platform-wide PGP key refresh completed. Key length requirements increased. Migration guide and verification steps documented.
READ MORE →
January 24, 2026
Decentralized Escrow Research: 2026 Security Implications
Academic researchers published findings on multi-sig escrow vulnerabilities and improvements. Practical implications for marketplace users reviewed.
READ MORE →
January 10, 2026
New Anti-Phishing Protocols Added to Nexus Market
Canary tokens, link verification hashes, and updated PGP-signed announcements deployed to combat phishing infrastructure targeting users.
READ MORE →
December 27, 2025
2025 Year in Review: Nexus Darknet Platform Evolution
A comprehensive retrospective on platform milestones, security upgrades, and ecosystem developments throughout 2025.
READ MORE →
December 13, 2025
Tor Browser 14.5: What Darknet Users Need to Know
Key security updates in Tor Browser 14.5 address timing-analysis vulnerabilities and fingerprinting mitigations. Full breakdown for marketplace researchers.
READ MORE →DRUG HARM REDUCTION: SAFETY INFORMATION
⚠ INFORMATIONAL CONTENT — NOT A GUIDE TO DRUG USE
The following harm reduction information is provided for educational purposes only, consistent with public health initiatives by organizations such as DanceSafe, the Drug Policy Alliance, and the WHO. If you or someone you know needs help, contact SAMHSA's National Helpline: 1-800-662-4357.
Harm reduction is a public health approach that acknowledges drug use occurs in society and prioritizes minimizing associated risks rather than solely advocating abstinence. Leading health organizations — including the World Health Organization and national public health agencies — publish harm reduction guidelines as a core component of drug policy.
✖ Never Use Alone
Having a trusted person present reduces the risk of fatal outcomes from accidental overdose. Inform someone of your location and substance use before starting.
📈 Test Your Substances
Fentanyl test strips and reagent test kits (Marquis, Mecke, Mandelin) can identify adulterants that cause the majority of overdose deaths. Never skip testing.
⚠ Start Low, Go Slow
Potency varies significantly between batches, even from the same vendor. Begin with a fraction of the intended dose. Tolerance changes are unpredictable.
💋 Avoid Polydrug Use
Combining substances — particularly depressants (opioids, benzodiazepines, alcohol) — dramatically multiplies overdose risk. Combinations account for most drug deaths.
🚑 Carry Naloxone
Naloxone (Narcan) reverses opioid overdose. It is available without prescription in most jurisdictions. Everyone who uses opioids should carry it. Learn how to administer.
🔒 Know Your Rights
Understanding local drug laws, possession thresholds, and legal protections is essential. Contact a harm reduction organization or legal aid service for jurisdiction-specific advice.
WHY OPSEC MATTERS FOR ANONYMOUS BROWSING
Operational security (OPSEC) refers to the set of practices that prevent adversaries from collecting information that could be used to identify individuals. For anyone researching or accessing the Nexus Darknet ecosystem, maintaining robust OPSEC practices is essential for personal privacy and security. Academic literature on darknet research consistently identifies OPSEC failures as the primary cause of identity exposure.
🔐 Tor Browser
The only recommended browser for accessing .onion services. Routes traffic through three encrypted relays. Never use a regular browser for darknet research. Download only from torproject.org.
🄯 Tails OS
An amnesic operating system that runs from USB, leaves no trace on the host machine, and routes all traffic through Tor by default. Recommended for high-security research.
📜 PGP Encryption
End-to-end encryption for all communications. GnuPG (GPG) is the standard implementation. Generate a dedicated key pair for darknet research — never reuse real-identity keys.
🚫 What to Avoid
Never enable JavaScript on .onion sites. Never use personal email, real name, or home address. Never reuse usernames across platforms. Never access via mobile networks without proper isolation.
WHAT DOES A LEGITIMATE NEXUS URL LOOK LIKE?
Phishing sites mimicking darknet markets account for a significant proportion of credential theft and financial losses in this ecosystem. Researchers at threat intelligence firms have documented hundreds of fake Nexus URLs designed to harvest login credentials. Understanding how to verify a legitimate onion link is a critical safety practice.
- All legitimate Nexus onion addresses are v3 (.onion) links — 56 characters long
- Official links are PGP-signed by the Nexus market admin key
- Never follow links from forums, Telegram, or Reddit without PGP verification
- Bookmark verified links directly in Tor Browser — never search for them
- If a site asks for 2FA before showing the captcha, it is a phishing site
Verify before you enter. All three official Nexus onion addresses are listed on the verified access page, alongside their PGP-signed confirmation. Cross-reference any link you intend to use against this verified list.
FREQUENTLY ASKED QUESTIONS
Nexus Darknet is an anonymous marketplace operating as a hidden service on the Tor network. It is accessible only through Tor Browser using verified .onion addresses. No clearnet version exists. The platform requires no personal identification from users, and all connections are routed through the Tor anonymity network by default.
Legitimate Nexus Market links are v3 onion addresses (56 characters). The most reliable verification method is to cross-check any link against PGP-signed announcements published by the platform's admin key. Never use links sourced from social media, forums, or clearnet search engines without PGP verification. Refer to our verified links page for confirmed addresses.
Monero (XMR) is the recommended cryptocurrency for the Nexus Onion platform and similar privacy-focused services. Unlike Bitcoin, Monero uses ring signatures, stealth addresses, and RingCT to make transactions untraceable by default. Bitcoin and Litecoin are also accepted but require additional privacy measures such as CoinJoin or wallet mixing to achieve comparable anonymity levels.
Reading publicly available information about darknet markets is legal in virtually all jurisdictions. Researchers, journalists, law enforcement professionals, and curious members of the public regularly study these platforms through open-source intelligence. This website contains no instructions for illegal activities and facilitates no transactions. All content here is informational and educational. Consult local legal counsel regarding jurisdiction-specific laws.
For secure darknet research, the essential tools are: Tor Browser (the only browser that should access .onion services), Tails OS or Whonix (operating systems designed for anonymous use), and GnuPG for PGP encryption. Additionally, a hardware-isolated research device, a dedicated Monero wallet for any transactions, and strict compartmentalization practices are recommended by security researchers. See the full OPSEC guide for complete details.
This resource covers all publicly documented aspects of the Nexus Darknet ecosystem — from platform architecture and cryptocurrency options to OPSEC best practices and harm reduction standards. Content is updated regularly to reflect the latest open-source research and security intelligence. All pages are provided for informational purposes only.